This guide will show how to configure Dataedo to work with a SAML identity provider. For this article, we'll be using Azure AD as the IdP, but similar steps can be taken for other providers too.
Initial configuration in Azure Portal (SAML provider)
Open Azure Portal and go to Enterprise Applications.
Choose the New application option:

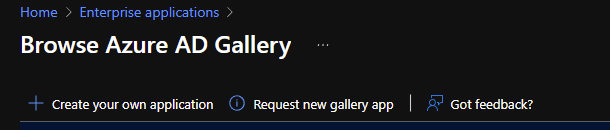
In the next window, choose the Create your own application option:
In the newly opened tab type in the application name for your internal use (I chose "Dataedo Portal") and click Create.

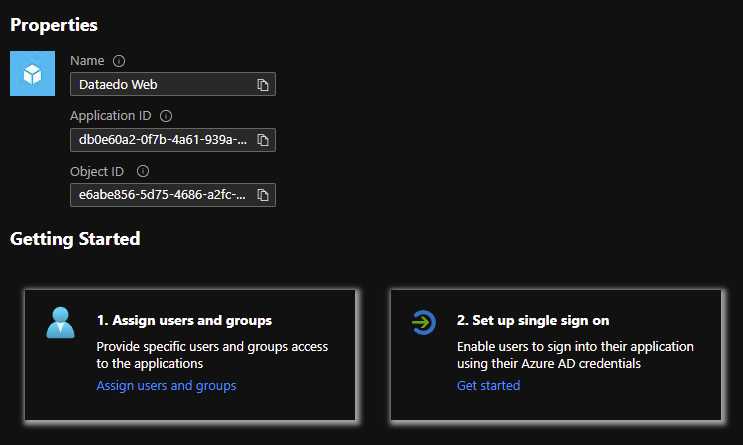
After a moment, you should see your new application screen. In the Getting started section, choose Assign users and groups.
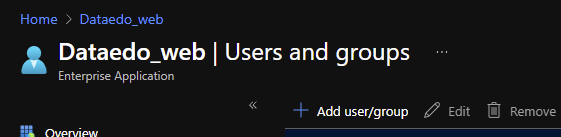
Now, use the Add user/group option to add user.
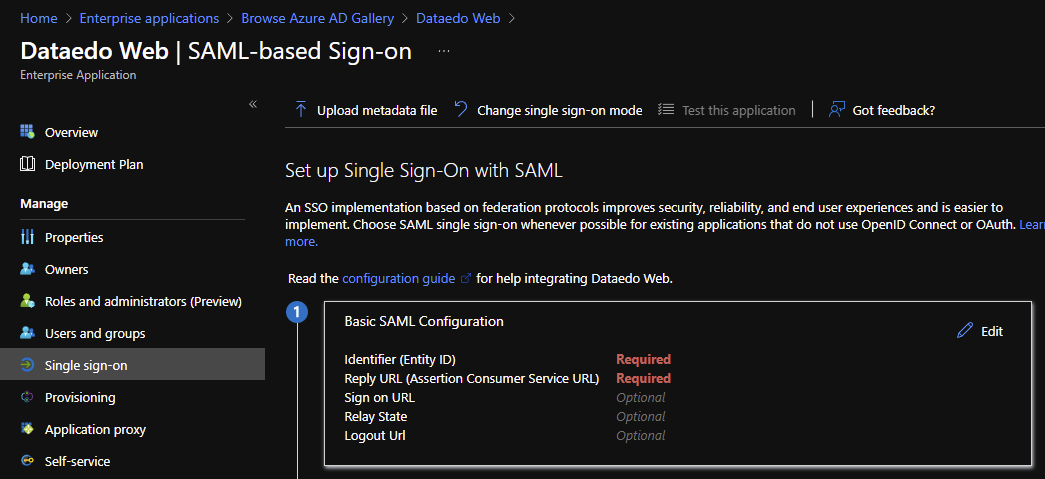
In the menu to the left, chooose Single Sign-on, then from the options to the right choose SAML.

Click Edit in the Basic SAML Configuration section.
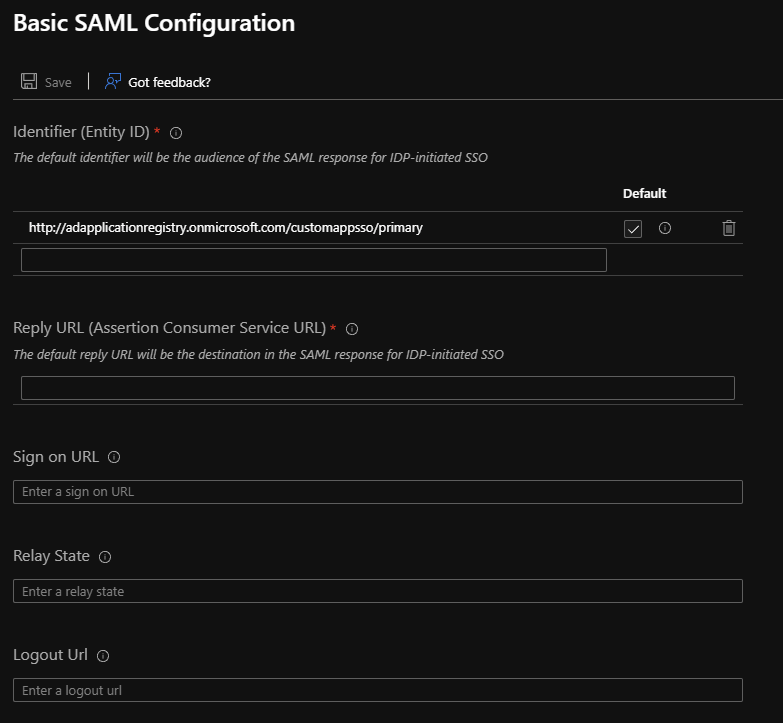
You should see a new tab, looking like this:
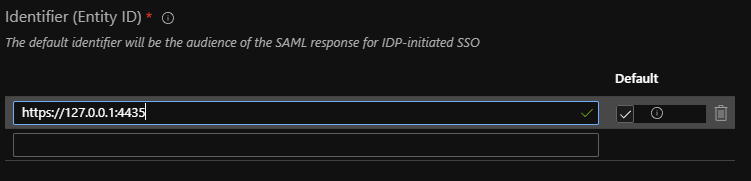
In the Identifier field, paste the address Dataedo Portal will be accessed with from your organization. Note that only HTTPS addresses are allowed.
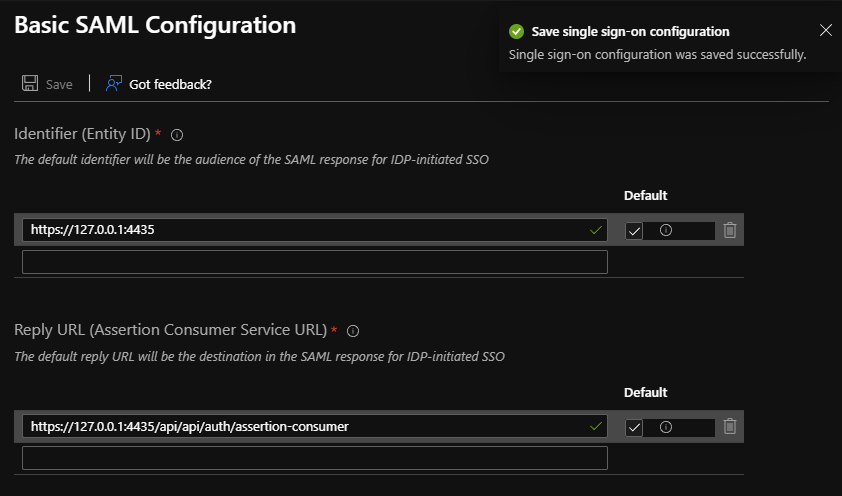
In the Reply URL section, type in the address your Dataedo Portal will be accessed on followed by /api/api/auth/assertion-consumer (for example https://your-Dataedo-Web.address/api/api/auth/assertion-consumer).

Click Save. The tab should now look like this:
Back in the Set up Single Sign-On with SAML tab on the left, find the SAML Signing Certificate section.

Copy the adress marked as App Federation Metadata Url - you will need it later.
Configuring SAML in Dataedo Portal settings file
Follow this section for Dataedo installed on a Windows machine.
Find the installation path of Dataedo Portal (default address is: *C:\Dataedo Web*), then go to Applications\API\ subfolder.
Right click and edit the appsettings.json file, and find the Saml2 section:
"Saml2": {
"IdPMetadata": "",
"Issuer": "",
"SignatureAlgorithm": "http://www.w3.org/2001/04/xmldsig-more#rsa-sha256",
"CertificateValidationMode": "ChainTrust",
"RevocationMode": "NoCheck"
},
Paste the App Federation Metadata Url link in the IdPMetadata field (alternatively, paste in the path for the metadata xml file).
In the Issuer field, paste the address specified before in the Identifier field in Azure (you can check it in Basic SAML Configuration > Identifier field in the application details in Azure Portal).
If required, correct the signature algorithm if you don’t use the default RSA_SHA256 algorithm - for example, for RSA_SHA1 the field should have the http://www.w3.org/2001/04/xmldsig-more#rsa-sha1 value.
Find the Saml2Client section:
"Saml2Client": {
"DisplayName": "",
"ClientUrl": "http://192.168.0.21:80"
},
Fill the DisplayName field – this will be the name shown when logging in to Dataedo for the Identity Provider.
Make sure the ClientUrl field correctly leads to your Dataedo Web address.
After changes, the edited parts should look like this:
"Saml2": {
"IdPMetadata": "https://login.microsoftonline.com/b411bcba-01b1-4de5-9fa1-45272da91a0c/federationmetadata/2007-06/federationmetadata.xml?appid=db0e60a2-0f7b-4a61-939a-56fbae2d8b8c",
"Issuer": "https://127.0.0.1:4435",
"SignatureAlgorithm": "http://www.w3.org/2001/04/xmldsig-more#rsa-sha256",
"CertificateValidationMode": "ChainTrust",
"RevocationMode": "NoCheck"
},
"Saml2Client": {
"DisplayName": "Azure AD SAML",
"ClientUrl": "https://127.0.0.1:4435"
},
Go to IIS Manager, and restart the Dataedo Web app for changes to take effect.
The next time you open Dataedo Web, you should have an option to login with Azure AD:
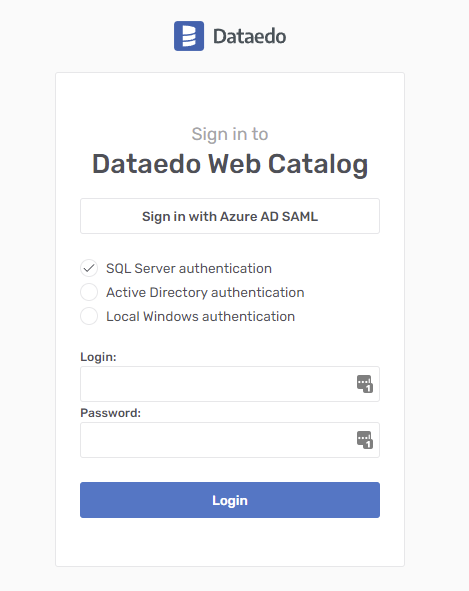
Clicking it will either take you to the Azure login page or if you’re already logged in, directly to your Dataedo Web page.
Configuring SAML in Dataedo Web Docker image
Follow this section for Web Catalog running from a Docker image.
Open .env file that should be located in same folder as docker-compose.yml file, find Single Sign On section:
#Single Sign On
DATAEDO_SSO_IDP_METADATA=
DATAEDO_SSO_ISSUER=
DATAEDO_SSO_SIGNATURE_ALGORITHM=http://www.w3.org/2001/04/xmldsig-more#rsa-sha256
DATAEDO_SSO_CERTIFICATE_VALIDATION_MODE=ChainTrust
DATAEDO_SSO_REVOCATION_MODE=NoCheck
DATAEDO_SSO_DISPLAY_NAME=
DATAEDO_SSO_CLIENT_URL=
Paste the App Federation Metadata Url link in the DATAEDO_SSO_IDP_METADATA field (alternatively, paste in the path for the metadata xml file).
In the DATAEDO_SSO_ISSUER field, paste the address specified before in the Identifier field in Azure (you can check it in Basic SAML Configuration > Identifier field in the application details in Azure Portal).
If required, correct the signature algorithm if you don’t use the default RSA_SHA256 algorithm - for example, for RSA_SHA1 the field should have the http://www.w3.org/2001/04/xmldsig-more#rsa-sha1 value.
Fill the DATAEDO_SSO_DISPLAY_NAME field – this will be the name shown when logging in to Dataedo for the Identity Provider. The DisplayName value cannot contain blank spaces (you can use underscore _ instead).
Make sure the DATAEDO_SSO_CLIENT_URL field correctly leads to your Dataedo Web address.
After changes, the edited parts should look like this:
#Single Sign On
DATAEDO_SSO_IDP_METADATA="https://login.microsoftonline.com/b411bcba-01b1-4de5-9fa1-45272da91a0c/federationmetadata/2007-06/federationmetadata.xml?appid=db0e60a2-0f7b-4a61-939a-56fbae2d8b8c"
DATAEDO_SSO_ISSUER="https://yourwebiste.com/"
DATAEDO_SSO_SIGNATURE_ALGORITHM="http://www.w3.org/2001/04/xmldsig-more#rsa-sha256"
DATAEDO_SSO_CERTIFICATE_VALIDATION_MODE=ChainTrust
DATAEDO_SSO_REVOCATION_MODE=NoCheck
DATAEDO_SSO_DISPLAY_NAME="Azure_AD_SAML"
DATAEDO_SSO_CLIENT_URL="https://yourwebiste.com/"
Update your Docker Compose with:
docker-compose up -d
The next time you open Dataedo Web, you should have an option to login with Azure AD:
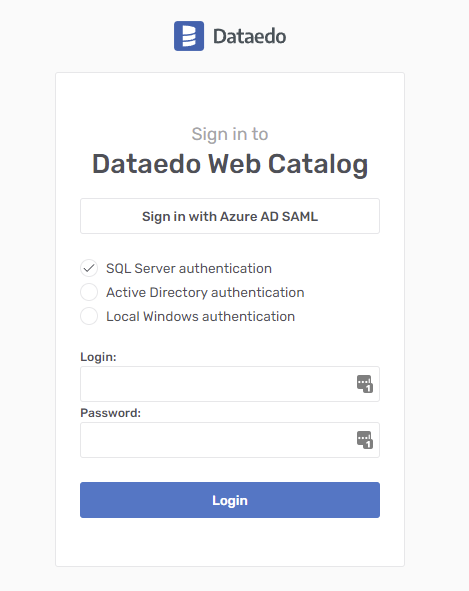
Clicking it will either take you to the Azure login page or if you’re already logged in, directly to your Dataedo Web page.










